 Front page > Programming > Proactive AppSec continuous vulnerability management for developers and security teams
Front page > Programming > Proactive AppSec continuous vulnerability management for developers and security teams
Proactive AppSec continuous vulnerability management for developers and security teams
What are some of the growing cybersecurity risks in the modern software development landscape that keep CISOs busy?
Developers and security teams face an ever-increasing array of threats, from sophisticated open source and vendor-controlled supply chain attacks to vulnerabilities introduced by AI-generated code like prompt injection and poor code security by GitHub Copilot. The complexity of modern applications, which often rely heavily on open source components (such as those you find on npm, PyPI, or RubyGems) and containerized deployments, adds to the challenge.
Given the scale and complexity of these risks, automating vulnerability management has become essential. Manual cybersecurity processes simply cannot keep up with the volume and velocity of potential vulnerabilities and software development. Automation not only speeds up the identification and remediation of security issues but also ensures that these processes, followed routinely by security teams, are consistently applied across all stages of the software development lifecycle.
The importance of continuous vulnerability management in specific domains
- Increasing reliance on open-source components: Open-source components have become ubiquitous in modern software development. While these components accelerate development for application developers and help reduce costs, they also introduce significant security risks. High-profile supply chain attacks, like the XZ backdoor and the SolarWinds breach, have highlighted the potential for widespread damage when vulnerabilities in open-source dependencies and closed vendor-controlled components are exploited.
- Growing use of AI-generated code in development: The rise of Generative AI (GenAI) in software development brings both opportunities and challenges. GenAI can significantly speed up coding tasks, but it can also introduce new vulnerabilities. AI-generated code may lack security considerations experienced developers typically include, leading to potential security gaps. One example of this is GitHub Copilot introducing an XSS in React.
- Rapid growth of containerized applications: Containerized apps have become the norm for deploying modern software. Containers offer numerous benefits, including consistency across environments and ease of scaling. However, they also introduce new security challenges, particularly in managing the vulnerabilities within container images. As such, developers could use help in educating them on how to choose the best container image and general container pro-tips, but automating the docker container image vulnerabilities is a must.
Let’s break these down a bit further… Another example of a high-profile supply chain attack is the attack on Codecov, where attackers gained access to sensitive data by exploiting vulnerabilities in a popular code coverage tool. A developer’s routine includes managing the risks associated with open-source dependencies. Open-source dependencies can introduce both direct and transitive vulnerabilities into your codebase. Direct vulnerabilities are found in the libraries you explicitly include, while transitive vulnerabilities exist in the dependencies of those libraries. Managing these risks manually is daunting, making automation a critical component of a robust security strategy.
With GenAI, AI code assistants like GitHub Copilot or ChatGPT introduce real, potential vulnerabilities. GenAI can inadvertently introduce insecure coding practices or fail to recognize context-specific security requirements. For example, an AI model might generate code vulnerable to SQL injection or cross-site scripting (XSS) attacks. Monitoring and securing AI-generated code is therefore crucial to maintaining application security.
The complexity of keeping up with new container vulnerabilities doesn’t escape security teams either. The rapid pace of new container vulnerabilities can be overwhelming. Each new vulnerability requires timely identification and remediation to prevent potential exploits. This complexity necessitates automated solutions with security expertise to manage container security effectively.
Container vulnerabilities can have a significant impact on the overall security of your applications. A single vulnerable container image can compromise the entire application stack. Tools like Snyk Container automate the process of identifying and remediating vulnerabilities in container images. Snyk Container can suggest new base image tags that minimize vulnerability counts and automate Pull Requests to update your code repositories.
How do we mitigate all of these AppSec cybersecurity threats?
Proactive AppSec and Continuous Vulnerability Management with Snyk
To mitigate the risks associated with AI-generated code, consider using tools like Snyk Code. Powered by Snyk DeepCode AI, this fast SAST tool can be integrated directly into a developer's IDE through a plugin. It uses security-specific data training to recognize vulnerable and insecure code, ensuring that issues are identified and addressed early in development.
Getting started with Snyk DeepCode AI is straightforward. The plugin supports popular IDEs such as Visual Studio Code, IntelliJ IDEA, VS Code, and PyCharm.
A quick guide to installing and integrating Snyk DeepCode AI in Visual Studio Code
- Install the Snyk extension:
- Open Visual Studio Code.
- Navigate to the Extensions view by clicking on the Extensions icon in the Activity Bar on the side of the window.
- Search for "Snyk" and click "Install" on the Snyk extension.
- Authenticate with Snyk:
- After installation, you will be prompted to authenticate with your Snyk account.
- Follow the on-screen instructions to log in or sign up here.
- Enable Snyk DeepCode AI:
- Once authenticated, navigate to the Snyk view in the Activity Bar.
- Enable Snyk DeepCode AI to start scanning your code for vulnerabilities.
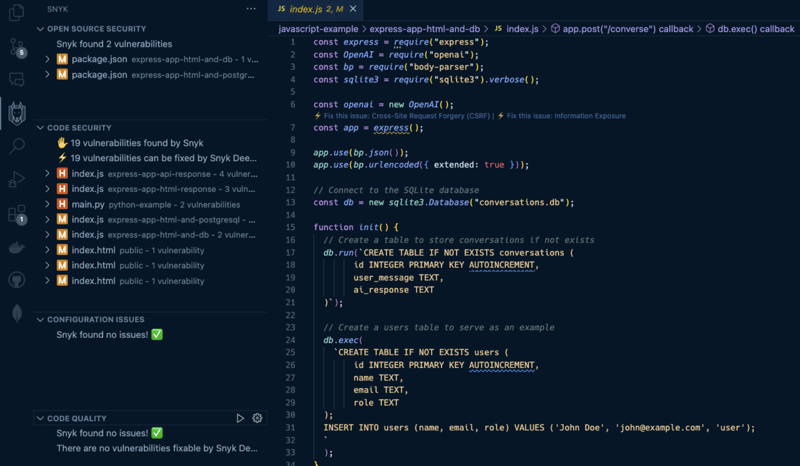
Once installed, the Snyk logo on the sidebar will feature vulnerabilities and security issues it found in your open-source dependencies, your own code (or GenAI-produced code), and IaC issues.
The benefits of SAST tools in identifying insecure code patterns right in the IDE for developers
- Real-time feedback: As you write code, Snyk DeepCode AI analyzes it in real time, providing instant feedback on potential security issues. This allows developers to address vulnerabilities before they become ingrained in the codebase.
- AI-driven insights: The AI model is trained on a vast dataset of security-specific data, enabling it to recognize insecure coding patterns, even those introduced by GenAI or poor programming practices.
- Seamless integration: By integrating directly into the IDE, Snyk DeepCode AI fits naturally into the developer's workflow, minimizing disruption and maximizing productivity.
Let’s see an example of mitigating vulnerabilities introduced by GenAI. I used GitHub Copilot in this project to auto-complete the code which creates an Express POST endpoint route to query the OpenAI API and then used res.send() to send the response to the browser.
However, what if the response in this payload were to be rendered directly in the browser? If the default text/html Content Type header was used to send this request, a Cross-site Scripting vulnerability would impact the running application. What can we do about this?
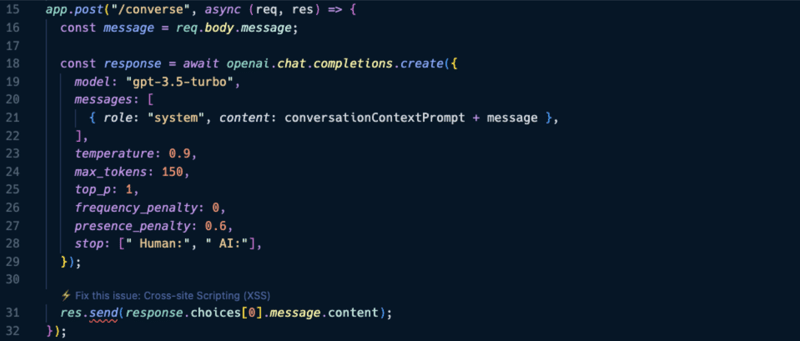
Well as you can see in the annotation above line 31, Snyk proposes to fix this security issue. I clicked on it and within a few seconds, the Snyk DeepCode AI extension proposed a mitigation that replaced the res.send() with res.json as follows:
res.json(response.choices[0].message.content);
With this change, the Express application forces the content-type in the response to be application/json which is generic text and can allow for text such as alert().
By leveraging Snyk in their IDE, developers can proactively identify and mitigate vulnerabilities using the underlying Snyk DeepCode AI engine, ensuring that their code is secure from the outset. This proactive approach to application security is essential in today's environment, where the risks associated with open-source supply chains and GenAI-generated code are ever-present.
Automating dependency management with Snyk Open Source
Snyk Open Source is a powerful tool designed to help developers and security teams manage the risks associated with open-source dependencies. With the increasing reliance on open-source libraries, the need for robust and automated dependency management has never been more critical. Snyk Open Source provides comprehensive vulnerability scanning and remediation capabilities, ensuring that your projects remain secure and compliant.
In my previous Node.js application, I also use an SQLite dependency, which Snyk alerts me of a security issue as follows:
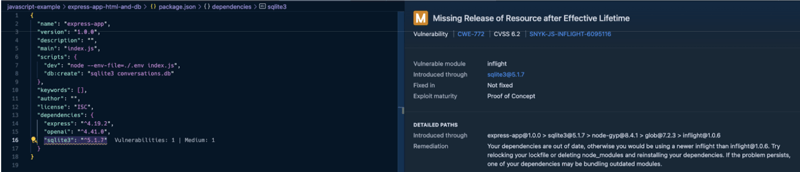
This vulnerability information is helpful to understand which transitive dependency is introducing the security risk and how to mitigate it, if at all possible. In this case, the transitive dependency inflight is detected to have a medium vulnerability.
Snyk detects that my lockfile and dependency is potentially out of date and so it can’t find a remediation path. However, let’s see the automation in practice when we import the GitHub code repository to Snyk. Doing so, shows the following information on the Snyk application:
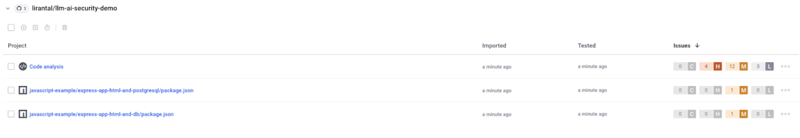
From this point on, Snyk will automatically open new Pull Requests to suggest dependency upgrades when security vulnerabilities are detected in my package manifest.
Managing dependencies is not just about the libraries you directly include in your project. Transitive dependencies—those pulled in by your direct dependencies—can also introduce vulnerabilities. Snyk excels at identifying and remediating vulnerabilities in both direct and transitive dependencies.
Consider the following scenario:
{
"dependencies": {
"express": "^4.17.1",
"lodash": "^4.17.20"
}
}
In this example, express and lodash are direct dependencies. However, express might have its own set of dependencies, which in turn might have their own dependencies. Snyk will traverse this entire dependency tree, identifying and addressing vulnerabilities at every level.
When it comes to managing container vulnerabilities, Snyk Container helps remove the burden of keeping base image tags up-to-date with security patches.
Snyk Container is a comprehensive solution designed to help developers and security teams manage container vulnerabilities effectively. Containerized application workloads is prevalent at the Enterprise and as is the need to secure these environments. Snyk Container integrates seamlessly into your CI/CD pipeline, providing continuous monitoring and proactive remediation of vulnerabilities in your container images.
One of the standout features of Snyk Container is its ability to automate the creation of Pull Requests to address vulnerabilities in your container images. This automation is a game-changer for both developers and security teams, as it significantly reduces the manual effort required to keep container images secure.
Here's an example of how Snyk Container might automate a PR to update a vulnerable package in a Dockerfile:
FROM node:14.1.0 RUN npm install express COPY . /app CMD ["node", "/app/index.js"]
When Snyk Container detects a vulnerability, it automatically generates a PR with the necessary changes to mitigate the issue. This could include updating a vulnerable package or applying a security patch. By automating this process, Snyk Container ensures that vulnerabilities are addressed promptly, reducing the window of exposure.
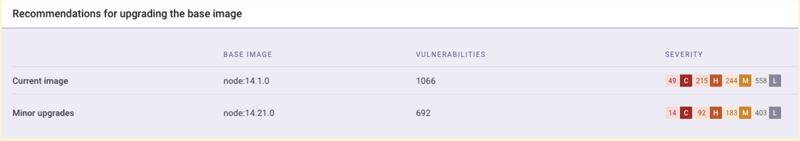
By following these recommended base images, you can significantly reduce the number of vulnerabilities in your container images, enhancing the overall security of your applications.
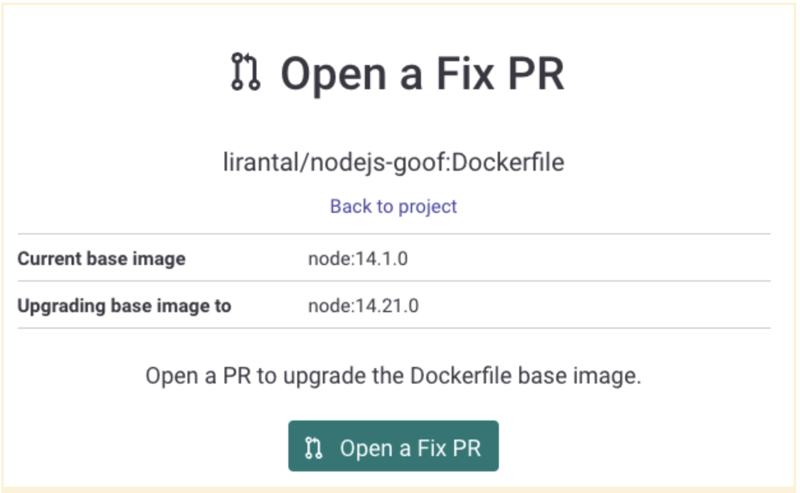
Snyk Container identified multiple vulnerabilities in this base image and automatically generated PRs to update the image and associated dependencies. The team was able to review and merge these PRs quickly, reducing their vulnerability count by over 30% within seconds by merging the Pull Request and ensuring the CI/CD pipeline tests pass with flying colors.

This proactive approach not only improved the security posture of their applications but also freed up valuable time for developers to focus on building new features rather than managing vulnerabilities.
-
 How to dynamically access global variables in JavaScript?Accessing Global Variables Dynamically by Name in JavaScriptGetting access to global variables during runtime can be a common requirement. Typically, ...Programming Posted on 2025-04-29
How to dynamically access global variables in JavaScript?Accessing Global Variables Dynamically by Name in JavaScriptGetting access to global variables during runtime can be a common requirement. Typically, ...Programming Posted on 2025-04-29 -
 How to Bypass Website Blocks with Python's Requests and Fake User Agents?How to Simulate Browser Behavior with Python's Requests and Fake User AgentsPython's Requests library is a powerful tool for making HTTP reque...Programming Posted on 2025-04-29
How to Bypass Website Blocks with Python's Requests and Fake User Agents?How to Simulate Browser Behavior with Python's Requests and Fake User AgentsPython's Requests library is a powerful tool for making HTTP reque...Programming Posted on 2025-04-29 -
 How to efficiently detect empty arrays in PHP?Checking Array Emptiness in PHPAn empty array can be determined in PHP through various approaches. If the need is to verify the presence of any array ...Programming Posted on 2025-04-29
How to efficiently detect empty arrays in PHP?Checking Array Emptiness in PHPAn empty array can be determined in PHP through various approaches. If the need is to verify the presence of any array ...Programming Posted on 2025-04-29 -
 VSCode shows the reason for CSS verification error in Go templateTroubleshooting CSS Errors in VSCode While Editing Go TemplatesWhen utilizing Go's html/template package and writing templates like mypage.tmpl, y...Programming Posted on 2025-04-29
VSCode shows the reason for CSS verification error in Go templateTroubleshooting CSS Errors in VSCode While Editing Go TemplatesWhen utilizing Go's html/template package and writing templates like mypage.tmpl, y...Programming Posted on 2025-04-29 -
 How do you extract a random element from an array in PHP?Random Selection from an ArrayIn PHP, obtaining a random item from an array can be accomplished with ease. Consider the following array:$items = [523,...Programming Posted on 2025-04-29
How do you extract a random element from an array in PHP?Random Selection from an ArrayIn PHP, obtaining a random item from an array can be accomplished with ease. Consider the following array:$items = [523,...Programming Posted on 2025-04-29 -
 How Can I Efficiently Read a Large File in Reverse Order Using Python?Reading a File in Reverse Order in PythonIf you're working with a large file and need to read its contents from the last line to the first, Python...Programming Posted on 2025-04-29
How Can I Efficiently Read a Large File in Reverse Order Using Python?Reading a File in Reverse Order in PythonIf you're working with a large file and need to read its contents from the last line to the first, Python...Programming Posted on 2025-04-29 -
 How to Check if an Object Has a Specific Attribute in Python?Method to Determine Object Attribute ExistenceThis inquiry seeks a method to verify the presence of a specific attribute within an object. Consider th...Programming Posted on 2025-04-29
How to Check if an Object Has a Specific Attribute in Python?Method to Determine Object Attribute ExistenceThis inquiry seeks a method to verify the presence of a specific attribute within an object. Consider th...Programming Posted on 2025-04-29 -
 Tips for implementing keyboard input timeout function in PythonWaiting for Keyboard Input with a TimeoutThe user input retrieval process can be time-consuming, especially when working with large amounts of data. T...Programming Posted on 2025-04-29
Tips for implementing keyboard input timeout function in PythonWaiting for Keyboard Input with a TimeoutThe user input retrieval process can be time-consuming, especially when working with large amounts of data. T...Programming Posted on 2025-04-29 -
 How to extract elements from 2D array? Using another array's indexUsing NumPy Array as Indices for the 2nd Dimension of Another ArrayTo extract specific elements from a 2D array based on indices provided by a second ...Programming Posted on 2025-04-29
How to extract elements from 2D array? Using another array's indexUsing NumPy Array as Indices for the 2nd Dimension of Another ArrayTo extract specific elements from a 2D array based on indices provided by a second ...Programming Posted on 2025-04-29 -
 How Can You Define Variables in Laravel Blade Templates Elegantly?Defining Variables in Laravel Blade Templates with EleganceUnderstanding how to assign variables in Blade templates is crucial for storing data for la...Programming Posted on 2025-04-29
How Can You Define Variables in Laravel Blade Templates Elegantly?Defining Variables in Laravel Blade Templates with EleganceUnderstanding how to assign variables in Blade templates is crucial for storing data for la...Programming Posted on 2025-04-29 -
 What is the difference between nested functions and closures in PythonNested Functions vs. Closures in PythonWhile nested functions in Python superficially resemble closures, they are fundamentally distinct due to a key ...Programming Posted on 2025-04-29
What is the difference between nested functions and closures in PythonNested Functions vs. Closures in PythonWhile nested functions in Python superficially resemble closures, they are fundamentally distinct due to a key ...Programming Posted on 2025-04-29 -
 How Can I UNION Database Tables with Different Numbers of Columns?Combined tables with different columns] Can encounter challenges when trying to merge database tables with different columns. A straightforward way i...Programming Posted on 2025-04-29
How Can I UNION Database Tables with Different Numbers of Columns?Combined tables with different columns] Can encounter challenges when trying to merge database tables with different columns. A straightforward way i...Programming Posted on 2025-04-29 -
 input: How Can I Efficiently Remove Multiple Spaces and Trim Leading/Trailing Spaces in Java? output: Java efficiently removes unnecessary spaces and end spacesJava: Replacing Multiple Spaces with Single Space and Trimming Leading and Trailing SpacesTo address the task of reducing multiple spaces to a single ...Programming Posted on 2025-04-29
input: How Can I Efficiently Remove Multiple Spaces and Trim Leading/Trailing Spaces in Java? output: Java efficiently removes unnecessary spaces and end spacesJava: Replacing Multiple Spaces with Single Space and Trimming Leading and Trailing SpacesTo address the task of reducing multiple spaces to a single ...Programming Posted on 2025-04-29 -
 How to pass exclusive pointers as function or constructor parameters in C++?Managing Unique Pointers as Parameters in Constructors and FunctionsUnique pointers (unique_ptr) uphold the principle of unique ownership in C 11. Wh...Programming Posted on 2025-04-29
How to pass exclusive pointers as function or constructor parameters in C++?Managing Unique Pointers as Parameters in Constructors and FunctionsUnique pointers (unique_ptr) uphold the principle of unique ownership in C 11. Wh...Programming Posted on 2025-04-29 -
 CSS strongly typed language analysisOne of the ways you can classify a programming language is by how strongly or weakly typed it is. Here, “typed” means if variables are known at compil...Programming Posted on 2025-04-29
CSS strongly typed language analysisOne of the ways you can classify a programming language is by how strongly or weakly typed it is. Here, “typed” means if variables are known at compil...Programming Posted on 2025-04-29
Study Chinese
- 1 How do you say "walk" in Chinese? 走路 Chinese pronunciation, 走路 Chinese learning
- 2 How do you say "take a plane" in Chinese? 坐飞机 Chinese pronunciation, 坐飞机 Chinese learning
- 3 How do you say "take a train" in Chinese? 坐火车 Chinese pronunciation, 坐火车 Chinese learning
- 4 How do you say "take a bus" in Chinese? 坐车 Chinese pronunciation, 坐车 Chinese learning
- 5 How to say drive in Chinese? 开车 Chinese pronunciation, 开车 Chinese learning
- 6 How do you say swimming in Chinese? 游泳 Chinese pronunciation, 游泳 Chinese learning
- 7 How do you say ride a bicycle in Chinese? 骑自行车 Chinese pronunciation, 骑自行车 Chinese learning
- 8 How do you say hello in Chinese? 你好Chinese pronunciation, 你好Chinese learning
- 9 How do you say thank you in Chinese? 谢谢Chinese pronunciation, 谢谢Chinese learning
- 10 How to say goodbye in Chinese? 再见Chinese pronunciation, 再见Chinese learning
























